Blockchain security company SlowMist said the North Korean APT hacker group was responsible for large-scale crypto and NFT phishing attacks that net the group roughly 300 ETH.
According to the report, the SlowMist began its investigations of the group in September after Twitter user PhantomXSec mentioned that the group was behind phishing attacks on multiple Ethereum and Solana projects.
SlowMist’s analysis of several phishing sites linked to the group showed that one of its primary tactics was to create fake NFT-related decoy sites with malicious mints. The group has almost 500 domain names that it uses for its phishing campaigns, some of which were registered over seven months ago.
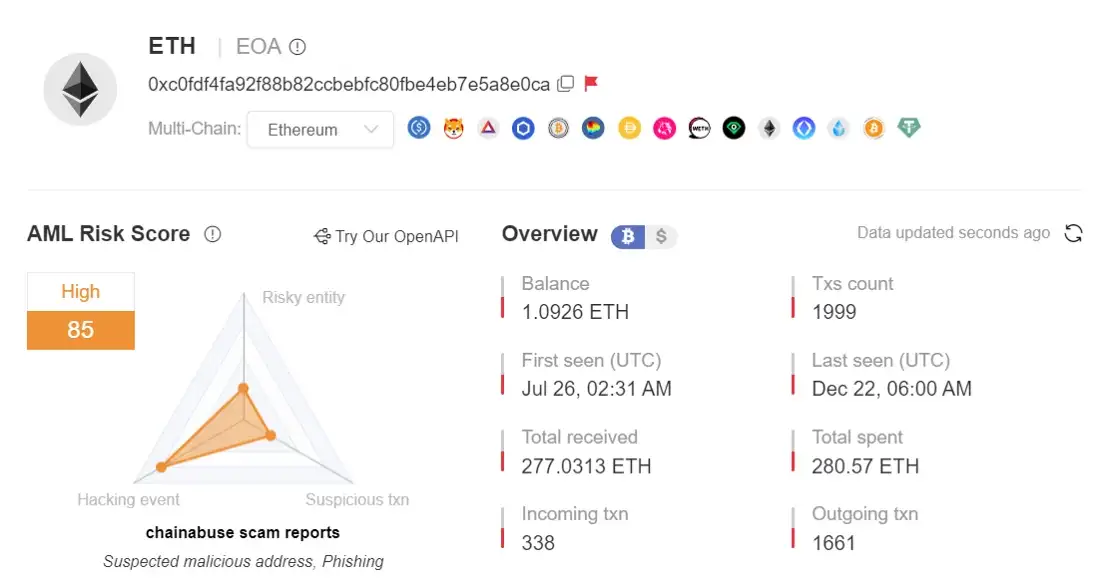
Wallet Linked to the Group Stole 1055 NFTs, Net 300 ETH
SlowMist revealed that a wallet linked to one of the phishing websites of the group received a total of 1,055 NFTs and made a profit of approximately 300 ETH through sales. According to the report, the wallet was initially funded through Binance. The report added that the wallet interacted with several risky addresses.
Additionally, several of the NFT phishing sites share the same host IP. There were 372 NFT sites under a single IP and another 320 phishing sites under another IP.
By examining the core code of the phishing sites, SlowMist discovered that the hackers used several tokens, such as WETH, USDC, DAI, and UNI, for the attack. The hackers usually focus on luring users to perform “Approve” operations.
But they sometimes go a step further to induce victims to “perform Seaport and Permit signatures, as well as other authorizing activities.” SlowMist also discovered a DeFi platform run by the North Korean hackers
Meanwhile, the security firm also identified some form of collaboration between North Korean and Eastern Europe hackers.
North Korea and Crypto Hacks
South Korea’s spy agency said North Korea-backed hackers have reportedly stolen over $1 billion worth of crypto assets since 2017. According to the report, the state-backed malicious players stole half of the amount in 2022 alone.
The South Korean agency said North Korea depends on crypto-hacking activities to fund its nuclear program and also to support its fragile economy.
Several reports have linked North Korean hacker groups like Lazarus to major hacks recorded in the industry this year. The group is reportedly responsible for the $100 million Harmony bridge exploit and the over $600 million exploit of Axie Infinitie’s Ronin bridge.











