By delving into the common mechanisms of crypto social media scams, this guide equips readers with the tools and knowledge to recognize and evade these traps. We explain some common scams alongside historical parallels that shed light on the underlying mechanisms of these scams. Read on to learn to navigate decentralized ecosystems safely.
Common crypto social media scams
Scams are nothing new. Each of the methods detailed below are merely variations on themes that have been around for centuries, if not longer. Yet the intersection of social media and cryptocurrency has formed a potent breeding ground for scams. Social media’s accessibility and broad reach make it a fertile arena for fraudsters. Meanwhile, the decentralized and often opaque nature of cryptocurrency offers a convenient cloak for deception.
Together, they create a “combustible combination.” In the words of the Federal Trade Commission (FTC), which reported that of the more than $1 billion lost to crypto scams in the 18 months to June 2022, almost half “started with an ad, post, or message on a social media platform.”
One in four people who reported losing money to fraud of any type identified social media as the starting point of their troubles. The growth of crypto scams is not merely a reflection of the rising popularity of digital currencies. It is also an indicator of the evolving sophistication of scammers.
Pump and dump schemes
“Pump and dump” schemes involve assets being artificially inflated in value only to be sold off for profit. The creation and promotion of small-cap cryptocurrencies, sometimes by celebrity influencers, provides fertile ground for manipulation.
The above is a typical pump and dump chart, in this case, EthereumMax, which was promoted by Kim Kardashian. Legal authorities have recognized the threat, with the Securities and Exchange Commission (SEC) cracking down on influencers who promote risky and unvetted tokens. In a series of charges in 2022 and 2023, celebrities and crypto entrepreneurs alike have faced legal scrutiny for their involvement in such practices.
Historical Parallel: This practice has been observed in various stock markets for centuries. Perhaps the most famous example is the South Sea Bubble in 1711. The South Sea Company inflated the value of its shares through false claims and speculation, only for it to collapse and lead to financial ruin for many investors.
Fake verification ticks
The blue verification tick on social media platforms such as Twitter, Facebook, and Instagram has come to symbolize trustworthiness and authenticity. However, this symbol of validation has been weaponized by scammers who manipulate these trust signals to their advantage. Exploiting the very emblem meant to instill confidence, scammers either acquire verified accounts or craftily incorporate a blue check into profile pictures and wallpapers to appear authentic.
Even with platforms like Twitter taking measures to shut down fake accounts, scammers still find ways to create convincing imitations. Recent instances include the surge of fake accounts following Elon Musk’s introduction of paid verification. This misuse of verification badges isn’t merely a deceptive aesthetic. It enables scammers to promote fraudulent projects, post phishing links, and sway investment decisions in crypto. This trend emphasizes the need for careful scrutiny of social media handles, even those with seemingly “verified” status.
Historical parallel: During medieval times, the forgery of royal and noble seals was a common way to fabricate the authenticity of documents. The Great Seal of the United Kingdom, for instance, had been counterfeited in attempts to forge royal decrees or land grants.
Fake applications
Fake apps pose as legitimate applications for cryptocurrency trading or as secure wallets. But these fraudulent apps serve as trojan horses for swindlers. Once downloaded, they may either stealthily install malware on the user’s device or directly steal funds deposited into the app. A sense of authenticity is often fabricated by distributing these apps through official channels. These might be the Apple App Store or Google Play Store.
The FBI’s 2022 fraud report underscores the gravity of this threat. In 2021, American investors lost approximately $42.7 million to criminals through deceptive applications. Fake crypto apps not only siphon money but also gather personal information that can lead to broader breaches of financial security. Awareness of this threat and the careful evaluation of an app’s legitimacy is crucial for anyone engaging in mobile cryptocurrency transactions, storage, or trading.
Historical parallel: The “snake oil” salesmen would travel across America selling fraudulent medicines that claimed to cure a multitude of ailments. The packaging, promotion, and presentation were all carefully designed to imitate genuine products. In reality, they contained no beneficial ingredients and were often harmful.
Romance scams
Romance scams, euphemistically termed “pig butchering,” are another form of scam that begins on social media. These often end in the irreversible transfer of crypto assets. The term “pig butchering” might seem oddly out of place in a financial context. Yet, it encapsulates an insidious form of crypto fraud that has gained traction in recent years. In these schemes, swindlers build trust with their victims (the “pigs”) over time, using social media, dating apps, or texting. Posing as successful traders, they promise to multiply life savings through crypto or forex trading. As the trust grows, so does the victims’ investment until the scammers vanish with the money – butchering them.
According to the FBI, pig butchering scams were responsible for over $429 million in losses in 2021. The demographic profile of victims reveals some surprising characteristics. Data shows that 67% are women aged 25-40, with an overrepresentation of graduate degree holders at 32%. Losses can be catastrophic, with 75% losing at least half their net worth and one-third being driven into debt.
The deception includes the creation of fake websites and apps that convincingly display the rapid growth of the victim’s investments. When they attempt to cash out, hurdles are placed in the form of taxes or fees. This further bleeds the unsuspecting targets.
How to avoid romance scams?
Avoiding these scams requires vigilance and skepticism. The FBI advises thorough due diligence on investment opportunities, careful evaluation of domain names, cautious downloading of apps or software, and a healthy dose of skepticism towards promises of guaranteed returns.
The rise of pig butchering scams underlines the evolving complexity of crypto-related fraud. It’s not merely the technology that requires understanding but human psychology and social engineering. These scams exploit trust, vulnerability, and greed. They are a reminder that the oldest tricks in the book can be dressed in the newest technological outfits.
Historical parallel: Casanova, the famous 18th-century figure, was known not only as a lover but also as a scam artist who utilized romance and charm to deceive and defraud. His memoirs document numerous financial schemes where he leveraged his personal connections.
Recognizing crypto social media scams
Recognizing fake influencer endorsements
The prevalence of social media influencers has created an environment ripe for exploitation through fake endorsements. In the crypto world, scammers may use doctored images or counterfeit profiles to mimic influencer support for various projects or products. Verifying influencer authenticity is, therefore, vital. This can be achieved by cross-referencing the influencer’s other social media platforms, checking for verification ticks, and being wary of suspicious activity like rapid follower growth. Common red flags may include inconsistent messaging, unfamiliar endorsement practices, or endorsements for products that don’t align with the influencer’s known values or interests. Sometimes, real influencers will still promote low-quality or outright scammy projects, so it’s important to always be careful when following these sorts of opaque endorsements.
Spotting fake apps
Identifying and avoiding fake apps demands careful scrutiny. Always download apps from reputable sources like official app stores and pay attention to details such as the developer’s name, company information, and application description. If anything appears suspicious, such as misspellings or mimicking well-known brands, it’s a signal to proceed with caution. Checking the developer’s website for authenticity and reading user reviews can further safeguard against accidentally downloading a fraudulent app that could compromise personal information or assets.
How to stay safe

1. Utilize a hardware wallet
Hardware wallets are physical devices that store private keys offline. They offer robust protection against online hacking attempts. By keeping the keys isolated from the internet, these devices create a barrier that is virtually impervious to theft. In most cases, an attacker would require physical access to the device, along with the passcode securing it, in order to steal the assets.
However, hardware wallets are not impervious to phishing attacks. If you grant permissions to a malicious contract, you may still find your assets gone. However, a hardware wallet requires physical confirmation of the transaction, so it gives some additional time to consider it before executing. Try to tell yourself why you’re submitting the transaction you’re about to submit. If you’re not sure, take a second.
2. Multi-signature wallets (with timelock)
Multi-signature wallets require multiple private keys to authorize a transaction. The integration of a timelock adds an additional layer of security. Timelocks can enforce a waiting period before a transaction is finalized, providing time to detect and counteract unauthorized actions. By requiring multiple approvals and incorporating time-based restrictions, the security level protecting one’s assets is strengthened, reducing the risk of unauthorized access.
3. Smart contract security audits
In a space where smart contracts play a pivotal role in transactions, engaging in security audits becomes paramount. These audits, often conducted by specialized third-party experts, scrutinize smart contract codes to identify vulnerabilities and ensure that they function as intended. Through a rigorous examination of potential weak points, these audits contribute to the secure and efficient operation of smart contracts within the decentralized landscape of crypto. An audit will point out if a contract is designed to scam users. However, it’s important to note that an audit cannot solve the vulnerabilities in a contract; it’s up to the developers to do that. An audit points out the red flags wherever they may exist.
General best practices
Getting involved with cryptocurrency demands critical thinking and a healthy degree of skepticism. Regularly updating and using legitimate security software, adhering to secure password practices, and utilizing only trusted exchanges and platforms are foundational to maintaining the integrity of one’s investments. In a space defined by innovation and transformation, the marriage of traditional wisdom with avant-garde technology paves the way for safe and confident participation in the crypto ecosystem.
Crypto social media scams are rife and growing
The confluence of cryptocurrency’s rise in prominence and social media’s ubiquitous reach has led to a proliferation of crypto social media scams. These scams are not isolated to crypto; they’re merely the application of old techniques to a new industry. From pump-and-dump schemes to the pernicious “pig butchering” frauds, the threat is real, multifaceted, and growing.
However, this should not overshadow the transformative potential of the crypto world or paralyze us with fear. Instead, it should serve as a call for education, vigilance, and the application of best practices. Utilizing tools such as hardware and multi-signature wallets can help safeguard assets and add a vital extra layer of consideration before sending any transaction. Coupled with a mindset grounded in critical thinking, secure habits, and continuous learning, these practices form a robust defense against scams. The historical parallels illuminate that what might seem novel or peculiar in the world of crypto scams can often be understood in the context of human history and behavior. By understanding the past, we can safely embrace the future.
Frequently asked questions
What is the scale of losses from crypto social media scams?
How are verification ticks misused on social media for scams?
What is a “pig butchering” scam?
What tools and practices can be used to stay safe from crypto scams?
About the author
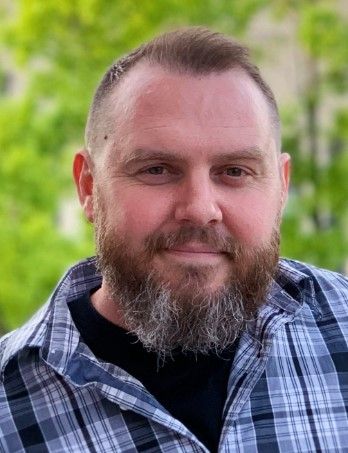
Hugh Brooks has worked in the security space for over 25 years, first as a U.S. Marine and then as an internationally recognized expert on cybersecurity, blockchain technology and security, and countering technology use by illicit actors. Hugh has built and consulted on successful products in tech startups around the globe for over a decade. He has multi-disciplinary experience in fields such as blockchain, social media, fintech, OSINT, big data, analytics, artificial and swarm intelligence, IoT, crypto, cybersecurity, and mobile security. He co-authored the book Using Social Media for Global Security and various papers on technology, crime, terrorism, and extremism. Hugh received his Master’s in Security Studies from Georgetown University and his BA from the University of Florida.















