Back in 2019, Heather Morgan gave a TED-style talk on “how to social engineer your way into anything” – now, along with husband Illyia Lichtenstein, she faces 25-years in prison over $4.5 billion worth of stolen Bitcoin dating back to the 2016 Bitfinex hack.
Earlier this week, Lichtenstein and Morgan were arrested in New York and charged with attempting to launder billions in bitcoin stolen by hackers from the 2016 hack that crippled Bitfinex, according to the U.S. Department of Justice. Those funds were seized by the DOJ, who intends to return the stolen bitcoin funds back to Bitfinex as well as the victims of the hack.
Was Morgan’s 2019 talk a reference to the Bitfinex hack?
Let’s flash back to 2019, when the New York-city couple gave a talk entitled “How to Social Engineer Your Way Into Anything” at NYC Salon.
During the half hour talk Morgan offers examples of powerful social engineering and infiltration techniques that can be used to manipulate someone into divulging information or taking action that ‘they otherwise would not’.
Despite the goofy awkwardness of her rapper alter-ego Razzlekhan, Morgan is in fact, a skilled and lucid orator. Her talk delights the New York audience who at several points break into spontaneous laughter or applause.
Is it possible that Morgan’s social engineering nous offer some clue as to how these funds were acquired in the first place?
It’s a theory that Eric Wall, Chief Investment Officer at Arcane Assets certainly prescribes to. In a Twitter thread on Wednesday, Wall speculated that the reason the precise nature of the Bitfinex exploit was never made public could be because the circumstances of the theft were ‘embarrassing’.
“People on [crypto Twitter] seem to have made their minds up that the hack happened in a very sophisticated technical manner, but there is no evidence of this,” said Wall. “And people also seem to forget just how potent social engineering can be, if you’re crafty.”
Wall suggests that had the theft been particularly technical then details would have been forthcoming since this would have helped Bitfinex ‘to absolve themselves from insider suspicions’.
It’s true that the exact nature of the exploit was never revealed, but recent events appear to have reignited old feuds and reopened old wounds.
BitGo blaming Bitfinex
To celebrate the occasion of Morgan and Lichtenstein’s arrest, key players from Bitfinex and their wallet provider of the time BitGo, decide to engage in a public Twitter spat.
BitGo CEO Mike Belshe made it clear that BitGo, “was not hacked or breached in the incident,” and instead places the blame on a Bitfinex, “breach across multiple systems and people.”
If the breach was socially engineered, the key element would of course be people. Zane Tacket, who was a community director at Bitfinex in 2016, had a few things to say about Belshe’s remark.
“Just so we are clear, are you saying that bitgo (systems or people) was not compromised at or around this time? No high level people, perhaps highest level of tech people, were hacked? They all used 2fa right?”
“We both know the root cause was a bitfinex system breach,” responded BitGo CEO Mike Belshe. “Bitgo would be excited to work with bitfinex to publish a full post mortem of the event.”
With temperatures appearing to rise, it’s unclear whether Belshe’s offer to publish a full post mortem was closer to a game of chicken than an act of conciliatory helpfulness. It may be the case that there is plenty of blame to share around.
It’s clear that with Bitfinex and BitGo both specifying people in their critiques of each other’s security, that some element of human error(s) and/or exploitation(s) were probably involved.

How to Social Engineer Your Way Into Anything
It’s August 2019 and Morgan holds the stage at an ‘NYC Salon’ event to present her people hacking event, “How to Social Engineer Your Way Into Anything.”
NYC Salon describes itself as ‘a speaker series that aims to be “TED with friends,”’ and describes the content of the event as follows:
‘Social engineering is the act of manipulating someone into divulging information or taking a particular action. While it often has a negative connotation in cybersecurity, there are many less sinister instances where you can use it to improve your life—from dating and job hunting to journalism, sales, and entrepreneurship.’
In particular the event organizers explained the types of expertise and experience that Morgan has:
‘Hear firsthand how Heather R Morgan social engineered her way into exclusive parties and expensive political fundraisers, infiltrated black markets around the world, and built relationships with celebrities and billionaire CEOs. You’ll learn actionable tactics for event crashing, how to cold email even the most reclusive and high-level people and get a response, and what to do to get yourself out of a jam.’
Morgan takes the mic and launches into one of her infamous raps, which includes the notorious ‘Crocodile of Wall Street’ line. Heather Morgan goes on to present herself as an expert in sales, cold emails and references her rap persona as well as her journalistic credentials.
“Social engineering is basically…I hate the term manipulating,” says Morgan in her opening address. “It’s getting someone to share information or take an action that they otherwise would not.”
Despite her disdain for the term, the process Morgan goes on to describe sounds a lot like manipulating.
Morgan lists some places she has socially engineered her way into including the Baron Palace in Egypt. She explains how after being caught by a security guard trespassing how she and a friend, with the help of a cigarette and bribe amounting to around $1 cash were able to persuade the guard to give them a tour.
Other exploits include crashing a Chinese wedding and appearing on a morning TV show.
Much of what Morgan presents is goofy and fun, and involves the sorts of exploits that would make for a fun anecdote at a dinner party, but it’s clear that there are some darker arts to ‘social engineering’ which Morgan is no stranger to.
“How are you going to influence [people]? It’s better to have more than one way. You can influence people a lot of ways, you can influence them with flattery, add value to them, you can bribe them…you can also influence them with fear,” adds Morgan. “Fear is a very delicate tactic. Fuck it up you’re gonna be screwed, they’re going to be angry, they might call the cops on you, but if you do it right and subtly it can work very, very well.”
Morgan reveals that one of her key infiltration techniques is to do research not only on the target company, but into the personal lives of individuals within that organization. Importantly she advocates for snooping on social media profiles to find out what kind of things those people like. This information can be useful for building rapport and quickly gaining a person’s trust.
The next big talk
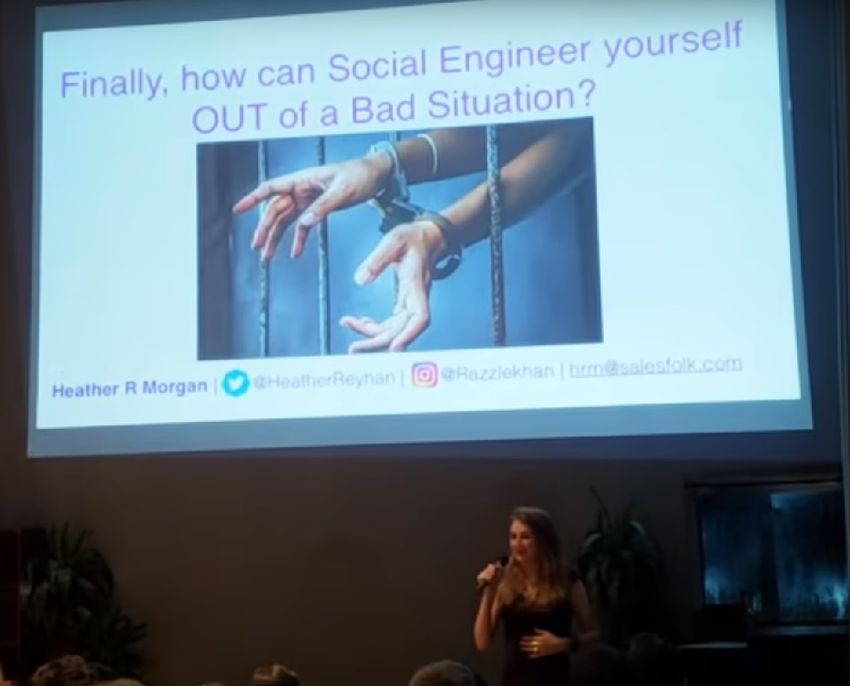
Morgan’s presentation ends with the final slide, “Finally, how can Social Engineer [sic] yourself OUT of Bad Situation?”
Ironically it is the one element of the talk which Morgan skips over, preferring instead to take questions from the audience. Given Morgan and Lichtenstein’s current predicament, perhaps it’s a topic the master manipulator might wish to revisit.
If the couple manage to evade jail time despite the attentions of the DOJ, the title of her next big talk should write itself.
What do you think about this subject? Write to us and tell us!











