Security researchers have identified a gas token scam targeting users of Binance Smart Chain (BSC).
The attack vector takes advantage of so-called gas tokens intended to help users save on gas fees. Although not the first time it has been observed, the attack has reemerged in response to the recent Multichain exploit.
Hackers Take Advantage of Users Revoking Multichain Approvals
The latest gas token scam appears to have arisen in response to various security tools prompting their users to revoke any unsolicited transactions. These prompts were issued in response to the recent Multichain bridge attack that stole around $126 million in crypto assets.
Read More: Best Crypto Sign-Up Bonuses in 2023
After news broke that Multichain’s Fantom bridge had been compromised, Multichain urged users to revoke all contract approvals related to the cross-chain bridging protocol.
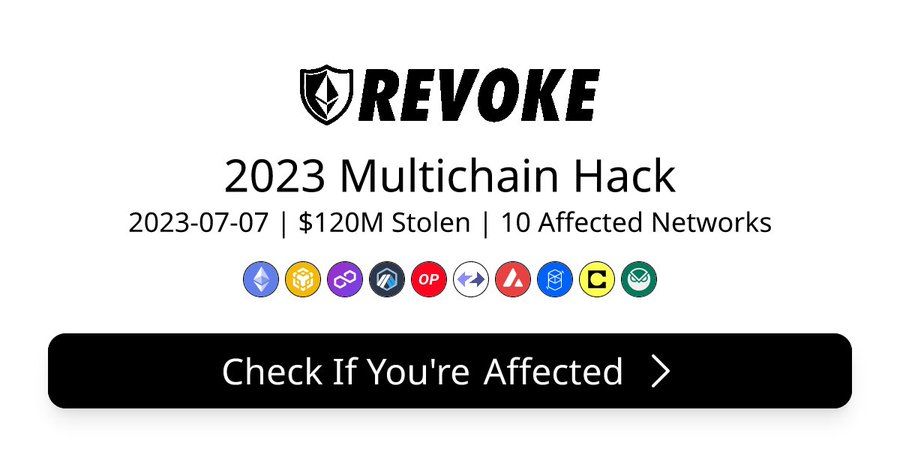
Following the announcement, security tool developers moved quickly to minimize their users’ exposure to risk. For example, the browser extension Revoke Cash recommended users revoke all Multichain approvals, as did the Rabby crypto wallet.
While developers issued such warnings to help protect users from potential threats, at least one hacker has taken advantage of the wave of revocations.
As the twitter user blanker.Eth first identified the scammer deployed a fake ERC-20 token on BSC that steals funds when users revoke the contract.
By using a fake contract, the scam minted CHI in victims’ wallets before transferring it to another address. But what exactly is CHI? And how was it used to bypass wallet defenses and steal crypto?
Gas Tokens Used to Siphon Funds
Developed by the team behind the 1inch DeFi protocol, CHI is what is known as a gas token.
The concept was originally developed to help Ethereum users lock in low gas prices to use later when they rose. Such tokens used a feature built into Ethereum that refunded gas fees when clearing storage. That is until a 2021 update made gas tokens redundant on the Ethereum mainnet by voiding the refund feature they exploited.
However, certain blockchains, including BSC, still implement the protocols deployed gas tokens. What’s more, other Ethereum-based blockchains could also be vulnerable to the attack. Although there is no evidence to suggest they are currently being exploited in this way.
Unfortunately, for BSC, the weakness appears to be a recurring issue. For example, BlockSec identified a similar scam back in January. And as long as the refund mechanism that gas tokens use remains in play, malicious actors will likely continue to exploit them.
Security Tools Respond to Gas Token Attack
After they were alerted to the latest threat, the developers behind Revoke Cash and Rabby moved quickly to respond.
Revoke Cash added a feature that disables revoking approvals if gas fees exceed a certain threshold. Rabby has implemented similar precautions.















