There are a variety of innovations that contributed to blockchain technology, one of the most important is hashing. But what is hashing in blockchain? Without it blockchains would be insecure, and altogether unusable. With it, they make cryptocurrency secure and reliable.
If you don’t want to get a computer science degree and would like to know the ins and outs of this cryptographic primitive, then stick around. You will find that the understanding hashing isn’t so hard.
What is cryptography?
The word cryptography comes from the Greek word kryptos, which means hidden. It is the study and application of methods for safe communication in the face of hostile activity. In essence, it is the act of encoding messages. Modern cryptography is computer centric but dates back to ancient times.
The Egyptian hieroglyphics are a great example of cryptography. Ancient Egypt developed the first encrypted messages as a series of disordered hieroglyphics, to prevent the uninitiated from learning the secrets of various mystery schools. This method of encryption was very simple, relying on a technique known as simple substitution.
Suspicious of his messengers, Roman Emperor Julius Caesar sent encrypted messages to his generals. Posthumously named, Julius Caesar popularized the Caesar Cipher. The Caesar Cipher is also a simple substitution technique.
What is hashing?
Hashing is a form of cryptography. A hash function is any function that can map arbitrary-size data to fixed-size values. Values returned by a hash function are called hash values, hash codes, digests, or simply hashes.
For instance, take the plaintext “Hello World.” Using the hashing function of Ethereum, Keccak-256 hashing function, we will convert the plaintext into the hash “592fa743889fc7f92ac2a37bb1f5ba1daf2a5c84741ca0e0061d243a2e6707ba.” Correspondingly, the output resembles an Ethereum address.
People unknowingly encounter hashes in their everyday lives. You may encounter hashes on a daily basis using passwords. When you create an account on an application, the provider more than likely does not save your password; they save a hash of your password. When you sign in to your account, the app hashes the password you enter and compares this hash to the hash it has saved on file.
Cryptographic Hash Function Properties
Simply put, not all functions are created equally. Hashing functions must satisfy specific requirements, in order to function properly. They must have the following properties:
Computationally efficient
Computers must be able to return the hash quickly; most can process a hash function in a fraction of a second.
Deterministic
For example, using the Keccak-256 hashing function, we will alter the message “Hello World” to “hello World”. This returns the value “079813c47d3d4ab9abf0c0747f5b5cdf90e0e264ae09ea44fb2509c559b72ac1.” As you can see, our hashing function is case-sensitive, and drastically alters the result of our returned hash.
The exact hash value must be produced every time for a given input value. You must remember that hashing is a way to securely send a message. If this were not the case, then you could alter the input to a hash, unbeknownst to the receiver.
Pre- Image Resistance
A pre-image attack occurs when a hash’s output is known and the task is to find some input. A pre-image attack on a cryptographic hash function seeks a message with a particular hash value. A cryptographic hash function should be resistant to pre-image attacks (set of possible inputs).
You would not want to use the pre-image (i.e. plaintext) as a password in our example “Hello World.” As the plaintext “Hello World” is extremely simple and easy to ascertain. There are databases that keep records of known inputs to even secure hash functions, like SHA-256.
Second Pre-Image Resistance
An expected property of a cryptographic hash function in which finding a second preimage of a known message digest is computationally impossible.
Collision Resistance
It must be extremely difficult, or impossible to find two inputs that produce the same output. Since the input value can be of any length, and any characters, the possibilities for this value are infinite. Outputs have a fixed length and —for that reason— a fixed number of possibilities.
It’s therefore possible for more than one input value to produce the same output. If the collision resistance isn’t strong enough, collisions could be found via a “birthday attack”. You may have noticed that second pre-image resistance and collision resistance are very similar. Rest assured that they are separate, and rather simple.
With second pre-image resistance, an input is known and the attacker is able to find a second input that hashes to the same value. With Collision resistance, both inputs are unknown, and the attacker is able to find both inputs that hash to the same value. Collision resistance implies pre-image resistance.
Birthday Attack
This is an attack that exploits the mathematics behind probability theory. You’ve probably heard of the birthday example; If you have a room of 27 people, although it seems unlikely, there’s actually a 50% chance of two people having the same birthday.

Why is this? One person has a 1/365 probability of having the ‘right’ birthday. The chance of a second person having that same birthday is also 1/365. To find the probability that both have the same birthday, we have to multiply their probabilities. So scaling up, if you have 365 different birthdays and therefore 365 possibilities, you need the square root of 365 which is 23 randomly chosen people for a 50% chance of people matching.
Applying this theory to hashing, we realise that technically; no hash function is collision-free, but with it should take a long time for this to occur!

How is Hashing used in Blockchain?
Bitcoin works on a blockchain and uses the hashing algorithm ‘SHA-256’ (Secure Hashing Algorithm 256). For bitcoin, hash functions are used for three mains functions:
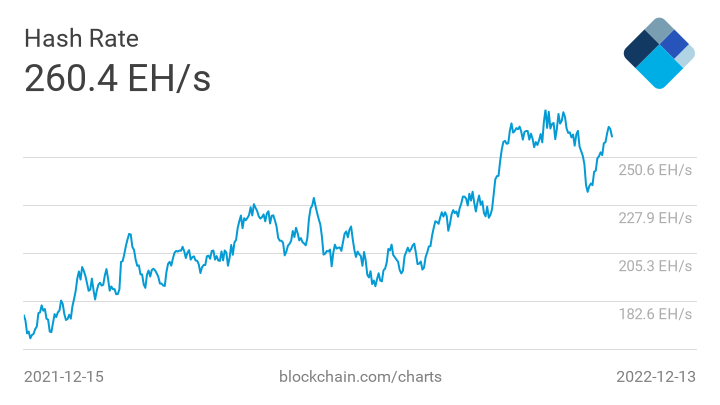
Mining
Miners race to solve a puzzle; each miner takes information from blocks they already know about, hash them, and builds a block out of them. If the output from the algorithm is smaller than the target number, then it will be considered valid and can be accepted by the rest of the network. They then have the right to create the next block.
Linking blocks
For added security; each block on the blockchain is linked to the previous one. This is achieved with a hash pointer (variables which store the address of another variable). Basically, each block contains the hash result from the previous block on the blockchain. This ensures that the history of the blockchain can be easily tracked and eliminates the possibility of a malicious block being added.
Creating keys
To send or receive cryptocurrency, you need a private and a public key. These two keys are connected to each other via a hash function. This is an essential component to ensure that nobody can work out your private key based on your public key.

The Importance of Hashing
The hash function gives cryptocurrency a high level of security. Although, in theory, nothing online is immune to hacking; the hash function provides the maximum difficulty level currently available.
< Previous In Series | Blockchain | Next In Series >















