With both lives and millions of dollars on the line, researchers face a massive bitcoin ransom to save their COVID-19 vaccine data.
Nothing Personal
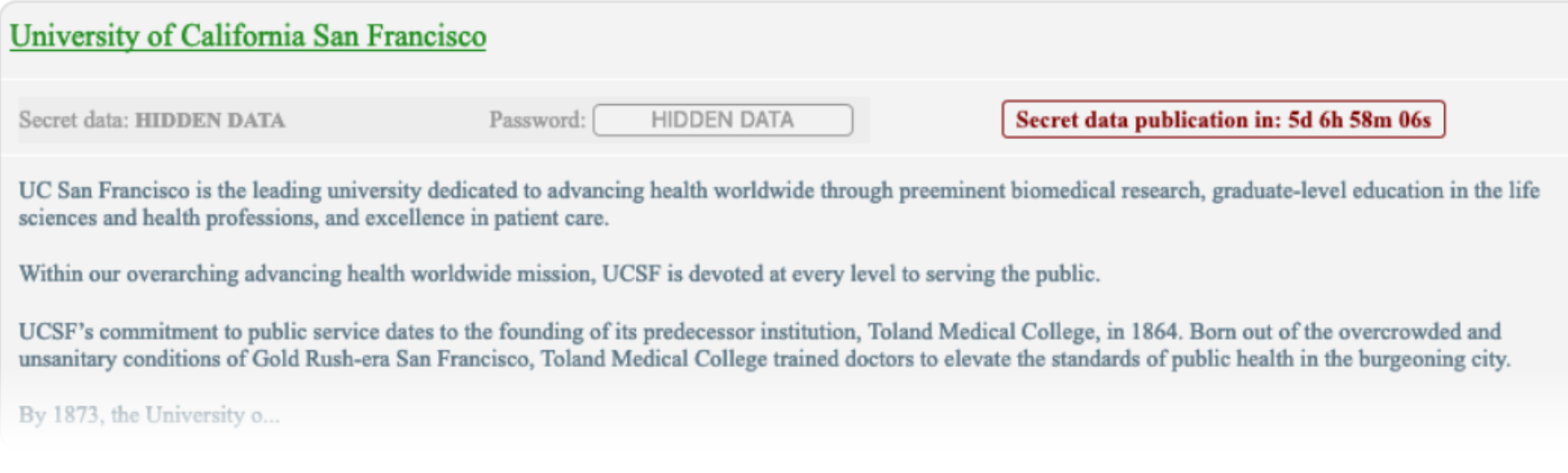
On June 5, researchers at the University of California San Francisco (UCSF) suddenly found their biostatistics data inaccessible. This included COVID-19 research, Bloomberg reported. The hackers had shut down their servers and demanded they visit a site on the dark web to begin negotiations.
They wanted $3 million dollars. With tens of millions, perhaps even billions of dollars on the line, the university had to take the threat seriously.
However, this was not the ransom of 20th-century gangsters. The hacker seemed to have an almost jovial tone. Though any security team is embarrassed by a breach, the Operator, as the hacker called himself, explained that the lab was just in the wrong place, at the wrong time.
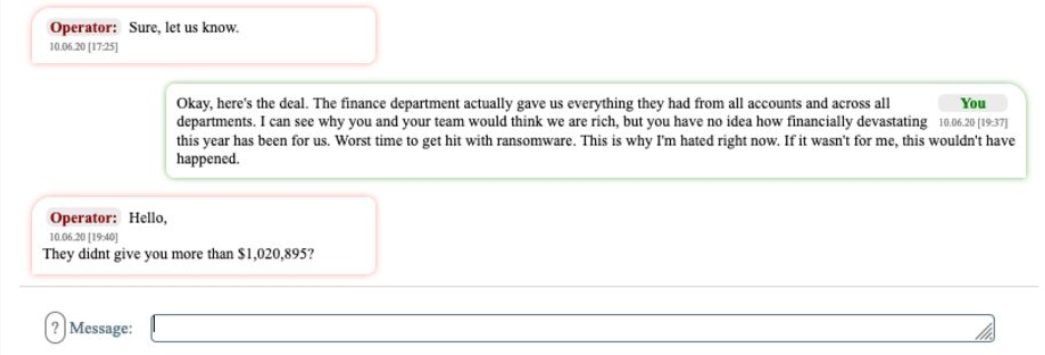
Though he first asked for $3 million, acquired transcripts reveal he was willing to negotiate:
My friend. Your team needs to understand, this is not your failure. Everything device with internet is vulnerable…You need to understand. For you as an big university, our price is shit.
Hacking With a Human Face
In contrast to individual hackers scouring the net on their own, today’s hackers are well organized. Some of these groups, according to the U.S. Department of Justice, spent 2019 professionalizing their modus operandi.
Groups of hackers are now working in a coordinated manner, targeting several victims at once. Some of them have front end websites, press releases, and statements about ethical standards.
The Operator who attacked UCSF sounded like he almost felt bad for his victim. Meanwhile, the dark web site, where the hackers sent their victims, looks almost like an online store checkout.
When originally offered $780,000, the hacker replied jokingly:
Keep that 780 K to buy Mc Donalds for all employers. Is very small amount for us. I am sorry.
Sorry? The days of rich family kidnapping to ruthless gangsters has turned corporate.
Business is Business, Even in Bitcoin
In the end, there is not much doubt about who the hackers are. Analysis of the Operator’s grammar is suggestive of Russian origin. He appears to be part of the growing hacking group called “Netwalker.” Interestingly, Cynet, an Israeli security group, said the group has prohibited English speakers from joining.
Another hacking group known as “Maze” made a statement of sympathy in a different incident:
We are living in the same economic reality as you are. That’s why we prefer to work under the arrangements and we are ready to compromise.
The ransom negotiations seem to be more like business negotiations. It appears to be the intimidation of organized crime with the distance and anonymity of the internet.
Flattery Will Get You Everywhere
The professional negotiator that the University brought in was able to push back. They also confirmed that it would be possible to restore the Biostat department’s servers. This gave them a little leverage. It proved that the hackers hadn’t just destroyed the servers and bluffed.
After several tough days, the negotiator fell back on flattery:
I have read about you on the internet and know that you are a famous ransomware hacker group and very professional. I know you will honor your word when we agree on a price, right?
These were the “magic words” that actually opened the hackers up to bargaining. Using more psychological tricks, the negotiator reduced the ransom to $1.14 million, which was paid with 116 bitcoin.
Stay Awhile
This particular attack comes at a time of increasing hacks. With so much on the line, professional hackers see an opportunity where victims have too much to lose. In May, the FBI reported that Chinese government hackers were targeting vaccine data.
The large crypto exchange Bitfinex recently offered hackers a $400 million reward for returning the $1.5 billion digital currency they stole in a 2016 attack. The hackers ignored this and even began moving the bitcoin to a new wallet.
Last month, a teenage hacker took control of several high-profile Twitter accounts and faked a charity drive to steal less than $200,000 in bitcoin.
As for the UCSF hack, when the negotiators asked for extra time, the hackers agreed if they could double the ransom. This was the move of a professional.
These attacks are unlikely to disappear soon. Just as cryptocurrency markets are open 24/7, so are hackers. Moty Cristal, a ransomware negotiator in Tel Aviv, said,
“There are no weekends off in a cyberattack.”











