A security researcher has discovered an unprotected database governing access to services from some of the world’s biggest tech companies. The database belongs to a short message service (SMS) routing operator responsible for sending two-factor authentication (2FA) codes to users of Meta, Google, and possibly crypto firms.
The researcher, Anurag Sen, found that the company’s YX International database was exposed without a password on the public internet. Anyone who knew the public internet protocol (IP) address could view the data.
Users Affected by Two-Factor Authentication Leak
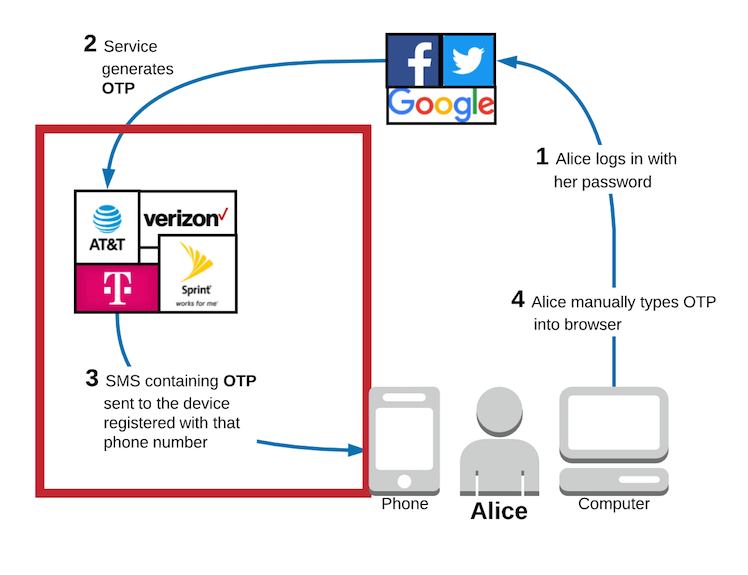
YX International sends security codes to people logging into platforms belonging to Meta, Google, and TikTok. The company ensures that users’ messages are routed speedily through mobile networks across the globe. Among the messages it sends are security codes that form part of a two-factor authentication scheme many large companies use to protect user accounts.
Some service providers, like Google, can send an SMS code to verify a user’s authenticity after entering a password. Other authentication options include generating a code from an authenticator app to complement a password.
Read more: 15 Most Common Crypto Scams To Look Out For
While two-factor authentication seeks to improve security, it is not a silver bullet. Accordingly, crypto exchange Coinbase warns that 2FA is a minimum security measure, but it is not foolproof. Hackers can still find a way to steal funds from crypto wallets.
“While 2FA seeks to improve security, it is not foolproof. Hackers who acquire the authentication factors can still gain unauthorized access to accounts. Common ways to do so include phishing attacks, account recovery procedures, and malware. Hackers can also intercept text messages used in 2FA,” Coinbase said.
Criminals Are Using These Methods to Beat 2FA
Last year, reports of criminals bypassing 2FA on Apple devices emerged. A hacker could access Apple’s cloud platform, iCloud, and replace a user’s phone number with their own. The scheme risked the funds in crypto wallet apps on Apple devices since some applications could have sent authentication codes to compromised phone numbers.
Criminals can also use SIM swaps to enact two-factor authentication crypto scams. In this line of attack, criminals convince mobile operators like AT&T or Verizon to transfer a phone number from the rightful owner to the fraudster. After that, the criminal only needs one other piece of information to access a self-custodial wallet app owned by the true owner of the phone number.
Given the surge in quantum technology, Apple recently improved the security of its Secure Enclave hardware device embedded in iPhones. The post-quantum cryptography scheme creates new keys every time a malicious actor compromises an old one.
This feature could help crypto wallet developers improve their clients’ crypto security by storing critical information in the Secure Enclave. So far, at least one vendor has already used the Secure Enclave to grant access to their wallet app.
Read more: What is a Private Key in Crypto?
BeInCrypto contacted Binance, the world’s largest cryptocurrency exchange, and Coinbase for comment on whether the XY International data leak affected their users. Neither company had responded by press time.















