Decentralized finance (DeFi) platforms Velodrome and Aerodrome front-ends were compromised twice in three days. The exploits resulted in a loss of funds and a decline in the total value of assets locked on Velodrome.
On November 29, the two platforms reported the first incident, stating that their front-ends had been compromised. These DeFi protocols urged users not to interact with the platforms pending the completion of investigations.
Velodrome and Aerodrome’s Domain Provider Issues
Velodrome and Aerodrome created an intel bounty on Arkham Intelligence, seeking information that could help identify the attackers. Investigations later revealed that the exploit was due to a social engineering attack on their domain provider. The DeFi platforms shared the information on November 30 and restored their original domains on December 1
However, some hours after the restorations, attackers targeted the domain provider again, prompting Velodrome and Aerodrome to urge users to avoid using the protocols yet again.
“It appears our provider has been exploited again. Please do not interact with our front-end,” Velodrome said.
Read more: Identifying & Exploring Risk on DeFi Lending Protocols
The domains have been restored as of press time. Still, the DeFI protocols now want to change providers to avoid a recurrence of the incident.
“The domain has been restored again and is locked at the TLD level pending transfer to a new provider,” Velodrome and Aerodrome said.
Velodrome Finance operates as an Optimism-based automated market maker. Aerodrome is its fork and the largest decentralized exchange on the Coinbase-backed layer-2 network Base.
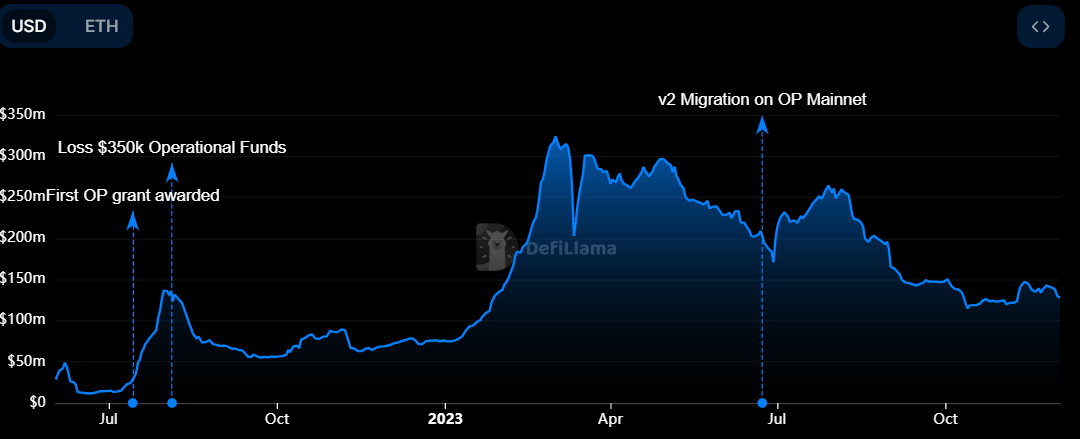
Total Value Locked Falls Following Front-End Attacks
Data from DeFiLlama shows that the back-to-back attack on Velodrome and Aerodrome’s front-end has affected their usage and TVL. Indeed, Velodrome’s TVL has fallen by more than $10 million since the incident began on November 29 to hit a low of $129 million as of press time.
On the other hand, Aerodrome has seen its TVL climb by around $5 million despite suffering the same attack.
Read more: Top 6 DeFi Lending Platforms
There are indications that some users of these platforms lost their funds to these attacks despite the repeated warnings. For instance, on-chain sleuth ZachXBT identified two addresses that received around $40,000 in stolen funds from the front-end attack.
Meanwhile, phishing scammers are allegedly taking advantage of the incident by creating fake verified accounts promising to compensate impacted users.















