A new cyber threat is emerging from North Korea as its state-backed hackers experiment with embedding malicious code directly into blockchain networks.
Google’s Threat Intelligence Group (GTIG) reported on October 17 that the technique, called EtherHiding, marks a new evolution in how hackers hide, distribute, and control malware across decentralized systems.
What is EtherHiding?
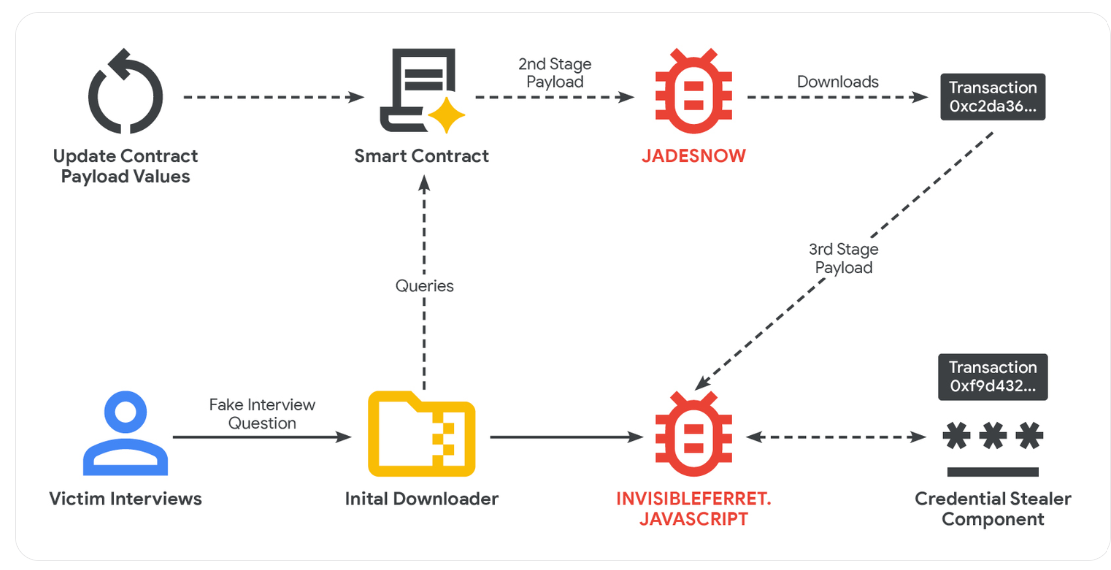
GTIG explained that EtherHiding allows attackers to weaponize smart contracts and public blockchains like Ethereum and BNB Smart Chain by using them to store malicious payloads.
Once a piece of code is uploaded to these decentralized ledgers, removing or blocking it becomes nearly impossible due to their immutable nature.
“Although smart contracts offer innovative ways to build decentralized applications, their unchangeable nature is leveraged in EtherHiding to host and serve malicious code in a manner that cannot be easily blocked,” GTIG wrote.
In practice, the hackers compromise legitimate WordPress websites, often by exploiting unpatched vulnerabilities or stolen credentials.
After gaining access, they insert a few lines of JavaScript—known as a “loader”—into the website’s code. When a visitor opens the infected page, the loader quietly connects to the blockchain and retrieves malware from a remote server.
GTIG pointed out that this attack often leaves no visible transaction trail and requires little to no fees because it happens off-chain. This, in essence, allows the attackers to operate undetected.
Notably, GTIG traced the first instance of EtherHiding to September 2023, when it appeared in a campaign known as CLEARFAKE, which tricked users with fake browser update prompts.
How to Prevent the Attack
Cybersecurity researchers say this tactic signals a shift in North Korea’s digital strategy from merely stealing cryptocurrency to using blockchain itself as a stealth weapon.
“EtherHiding represents a shift toward next-generation bulletproof hosting, where the inherent features of blockchain technology are repurposed for malicious ends. This technique underscores the continuous evolution of cyber threats as attackers adapt and leverage new technologies to their advantage,” GTIG stated.
John Scott-Railton, a senior researcher at Citizen Lab, described EtherHiding as an “early-stage experiment.” He warned that combining it with AI-driven automation could make future attacks much harder to detect.
“I expect attackers to also experiment with directly loading zero click exploits onto blockchains targeting systems & apps that process blockchains… especially if they are sometimes hosted on the same systems & networks that handle transactions / have wallets,” he added.
This new attack vector could have severe implications for the crypto industry, considering North Korean attackers are significantly prolific.
Data from TRM Labs shows that North Korean-linked groups have already stolen more than $1.5 billion in crypto assets this year alone. Investigators believe those funds help finance Pyongyang’s military programs and efforts to evade international sanctions.
Given this, GTIG advised crypto users to reduce their risk by blocking suspicious downloads and restricting unauthorized web scripts. The group also urged security researchers to identify and label malicious code embedded within blockchain networks.

