Hacken’s Q1 2026 Security & Compliance Report puts the quarter’s losses at $482.6 million. Earlier figures covered incidents only through March 22. A social engineering scam on March 31 added another $18.2 million and pushed the final quarter total 20.9% above Q4 2025.
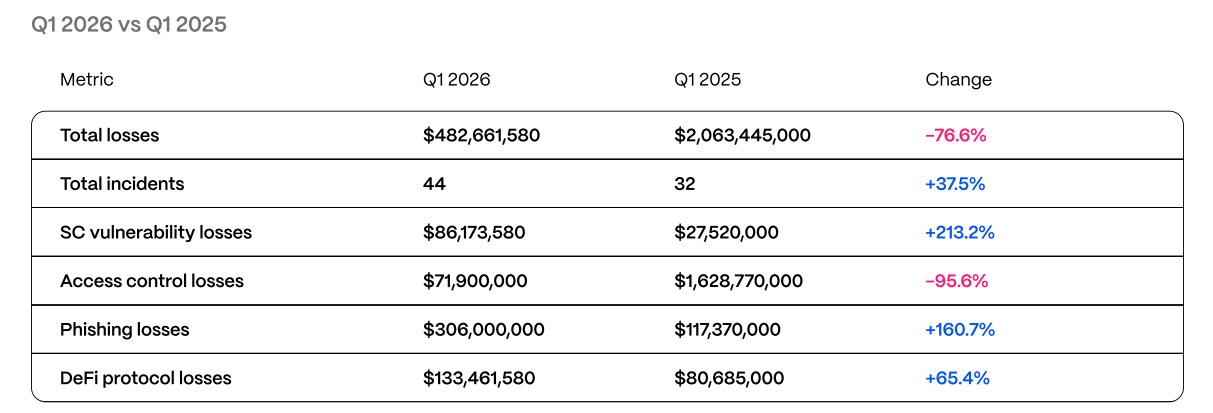
The attack mix is worth noting. Phishing and social engineering drove $306 million in losses, or 63.4% of the total. One hardware wallet scam alone accounted for $282 million. For all the attention crypto gives code risk, user manipulation remained the biggest source of damage in Q1.
Social engineering still beats technical defenses
In Q1, the largest damage came from deception, stolen trust, and access abuse.
A user does not need to face a sophisticated contract exploit to lose funds. A fake support interaction, a poisoned link, or a stolen recovery phrase can do enough damage on its own. Q1 offered another reminder of how expensive those failures remain.
Smart contract exploits also rose sharply
Smart contract exploits still formed a major share of quarterly losses. Hacken puts contract-related damage at $86.2 million across 28 incidents, up 213% year over year.
The report says six audited protocols were exploited during the quarter. One had already gone through 18 audits. Audit coverage still helps, but the Q1 figures show audit work alone does not keep a protocol safe over time.
Audits help, but follow-through decides outcomes
The divide in crypto security often comes down to how teams operate after review work is complete.
In Hacken’s figures, exploited audited protocols averaged $6.3 million in losses per incident, versus $4.3 million for unaudited ones.
Indeed, teams often secure an audit, then keep shipping upgrades, changing permissions, adding dependencies, or expanding access without enough follow-up review.
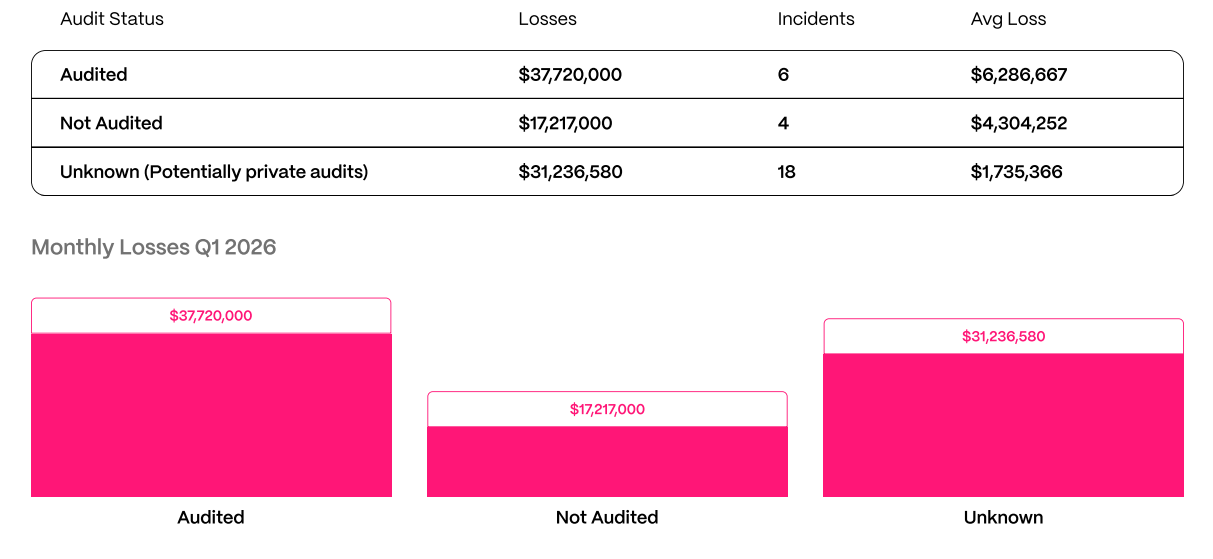
Security works best as an ongoing discipline inside product development, access control, treasury management, and incident response.
Beyond protocol exploits
Hacken’s report includes views from KuCoin, MEXC, WhiteBIT, Bybit, Centrifuge, Global Ledger, Allium, SovereignAI, M0, C4, and Gray Wolf.
For example, in the extract below, Hacken asked KuCoin how PoR is evolving into regulatory infrastructure.
Exchanges, compliance specialists, analytics firms, and protocol teams all view risk through different filters. Even so, the report points to the same conclusion. Web3 security depends on code quality, internal controls, wallet safety, monitoring, and operational discipline across the full scope of activity around a product.
DPRK-linked tactics stayed effective
The report also points to continued use of familiar attack methods by DPRK-linked actors.
According to Hacken, fake investor calls, malicious software updates, and compromised employee devices remained effective tools in Q1. Those methods reportedly helped extract more than $40 million from Step Finance and Bitrefill during the quarter.
The continued success of these tactics says a lot about how exposed many teams still are at the human and organizational level.
Stablecoins and AI add new pressure points
The report also spends time on stablecoin design and AI-related risk. On stablecoins, Hacken says 38.5% of audited projects it reviewed had compliance mechanisms in code which were not enforced across all execution paths.
On AI, Hacken says Q1 included the first major exploit involving AI-written smart contract code. It also highlights wallet signer abuse, MEV exposure, and other risks tied to AI-assisted systems.
Final thoughts
Hacken’s Q1 report shows a market where old weaknesses still cost the most. Human error, access abuse, and social engineering produced most of the quarter’s losses. Smart contract exploits added another large share. Audits remained useful, yet outcomes still depended on what teams did after audit completion.











